⚠ The Post-Quantum Threat
Your Encryption
Has an Expiration Date
Post-quantum computing represents one of the greatest challenges to information security in modern history. Post-quantum computers, with their ability to perform complex calculations at speeds unimaginable for classical systems, have the potential to break the current cryptographic systems that protect virtually all of our digital infrastructure.
Shor's algorithm, developed in 1994, theoretically demonstrated that a sufficiently powerful post-quantum computer could break RSA and ECC encryption systems — fundamental pillars of internet security. This means that practically all current security systems — from banking transactions to confidential government communications — is already obsolete.
- RSA and ECC encryption is already obsolete
- Banking transactions vulnerable to post-quantum attacks
- Government communications at risk
- 'Harvest now, decrypt later' attacks are already happening
2026
Cryptographically relevant post-quantum computers are here.
100%
Of current encryption at risk.
All
Digital infrastructure affected.
Now
Adversaries harvesting encrypted data.
"
"Any hardware (including servers) or software that is not post-quantum is already obsolete. And that affects the ENTIRE economy and public administration."
This situation creates a critical window of opportunity for PhotonicGuard, allowing us to position ourselves as leaders in providing solutions that protect confidential information against these emerging threats, setting a new security standard for the post-quantum era.
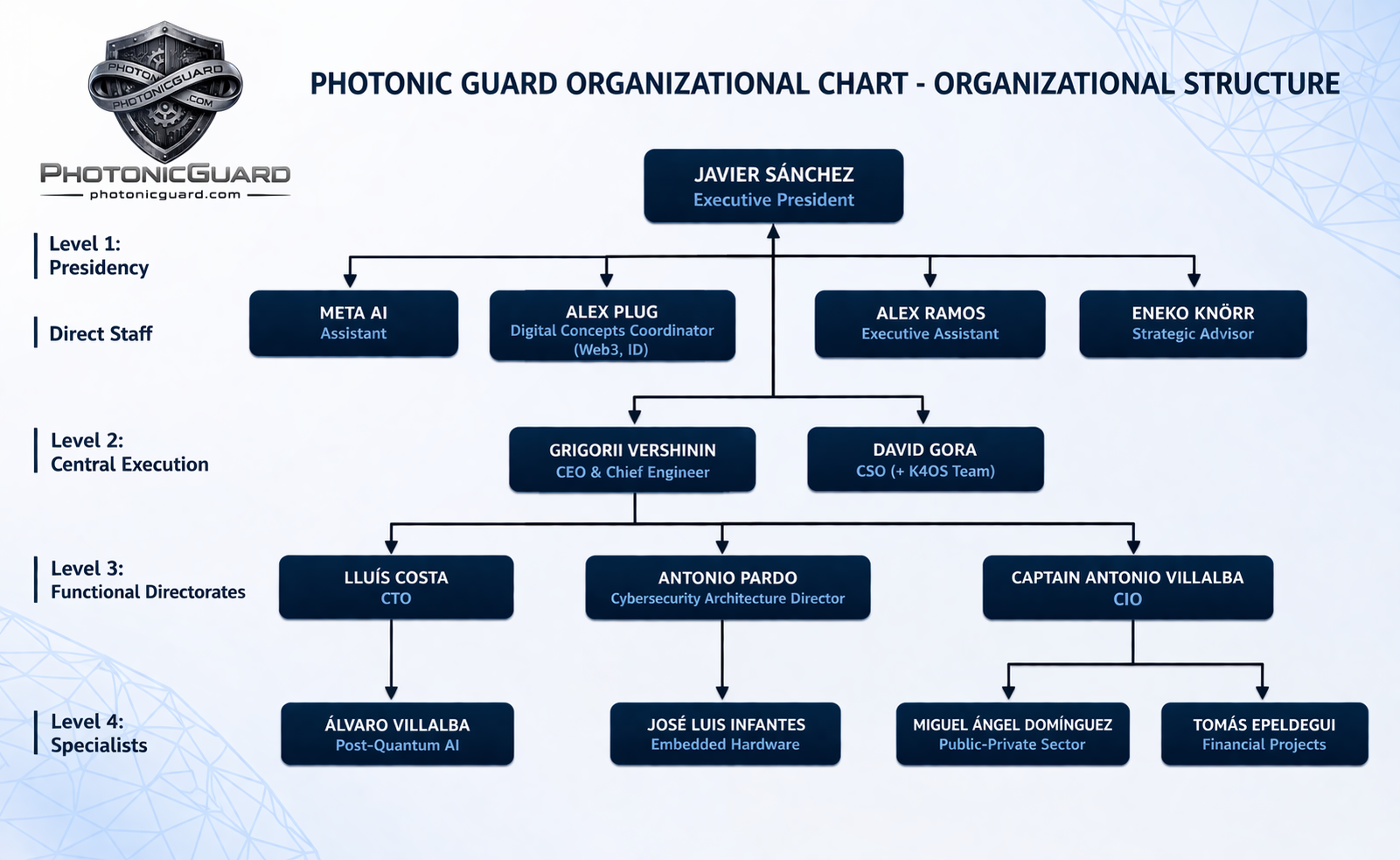
Organizational Chart
What Defines Us
Principles that guide our mission to secure the post-quantum era
Innovation
We are at the forefront of post-quantum cryptography research, constantly advancing the state of the art to stay ahead of emerging threats.
Protection
Our unwavering commitment is to protect organizations against quantum-capable adversaries before the threat becomes critical.
Excellence
We deliver world-class post-quantum solutions built on rigorous science, engineering, and security standards.
Transparency
Open communication with our clients about threat landscapes, timelines, and the best protective measures available.
Collaboration
We partner with governments, enterprises, and research institutions to build a post-quantum secure ecosystem.
Urgency
We understand that the post-quantum threat is not future — it is present. We act and advise accordingly.